Because of the COVID-19 p[l]andemic, many people turned to online transactions and digital payments much more than they used to. However, this shift towards a cashless society has also raised concerns about the security of personal data, especially in a country like India where data breaches are not uncommon. During this time, there have been reports of data leaks involving Indian cardholders, highlighting the importance of safeguarding privacy in the digital age.
With the lockdowns and restrictions imposed during the pandemic, many people turned to online shopping and contactless payments as a safer alternative to traditional cash transactions. This led to a surge in the use of digital wallets, payment apps, and online banking services. While this shift was convenient for many, it also exposed vulnerabilities in the security of online transactions.
One of the major drawbacks of going completely cashless is the risk of data breaches and leaks. The incidents involving Indian cardholders’ data being exposed have raised concerns about the security of online payment systems. Hackers and cybercriminals are constantly looking for ways to exploit vulnerabilities in digital platforms, putting consumers at risk of identity theft and financial fraud.
As the use of artificial intelligence (AI) in financial services continues to grow, there is a debate about the role of AI in ensuring the security of digital transactions. While AI can be a powerful tool for detecting fraud and mitigating risks, there are also concerns about the potential for bias and discrimination in AI algorithms.
In the face of such risks, many individuals have started to question the push towards a cashless society. With the convenience of digital payments also comes the vulnerability of data breaches. As a result, some are advocating for a return to cash transactions as a way to safeguard their privacy and security.
Relying too much on digital payments and AI technologies introduces various challenges. One of the most pressing issues is the increased risk of data breaches and cyber attacks, which can endanger sensitive information and lead to financial setbacks. The Department of Telecommunications has recently instructed telecom providers to broadcast cybercrime awareness tunes 8-10 times a day for three months, illustrating the seriousness of this issue. In light of this, cash transactions are more important than ever.

Cash continues to be a relevant form of payment in our increasingly digital society. While the ease of online transactions is undeniable, many people still value the security that cash brings. The physicality of money provides a sense of control and privacy that digital transactions often fail to deliver.
When crises or emergencies strike, cash transactions emerge as a reliable payment method, free from the constraints of technology or infrastructure. As worries about data leaks and cyber threats escalate, many individuals are embracing cash as a trusted and secure option for their financial transactions.
“Dark Web Leak of Over 100 Million Debit and Credit Cardholders”
• Data leaked via faulty server of mobile payments company Just Pay.
• Leaked information includes names, phone numbers, email addresses, and card digits.
• Juspay processes payments for Amazon, MakeMyTrip, Swiggy, Google, Microsoft, Visa, Mastercard, American Express Global Business Travel, and prominent financial institutions
JUSPAY is a global leader in enterprise payment solutions, powering payments for merchants and banks worldwide.
Founded in 2012 in Bangalore, backed by prestigious investors including SoftBank, Accel, and VEF, our team of 1,200+ payment experts operates from innovation hubs across Bangalore, Dublin, São Paulo, San Francisco, and Singapore.
According to Gadgets 360, a troubling data leak on the dark web has exposed information related to debit and credit card transactions that occurred between March 2017 and August 2020. The leaked data includes cardholder names, customer IDs, and the first and last digits of the cards.
This discovery was made by cybersecurity researcher Rajshekhar Rajaria just a week prior. In light of this situation, Juspay has responded, stating they are working closely with the appropriate government bodies and the RBI.
Nearly One Billion Emails & Personal Details Leaked from Verifications.io, Source was Picasa API?
The Daily Mail and Forbes reported that personal information from 982 million email accounts included names, gender, dates of birth, employers and even residence in the database. Good news was that the info did not contain passwords or credit card details.’
Forbes: https://www.forbes.com/sites/daveywinder/2019/03/10/2-billion-unencrypted-records-leaked-in-marketing-data-breach-what-happened-and-what-to-do-next/
The online email database was created by a company called Verifications.io, which reportedly had no security measures in place. The company offered an “enterprise email validation” service for marketing companies to check whether email addresses were valid or not. Security Researcher Bob Diachenko discovered the breach in an online database created by Verifications.io that had no privacy protections in place.
What happened to Verifications.io after the data leak?
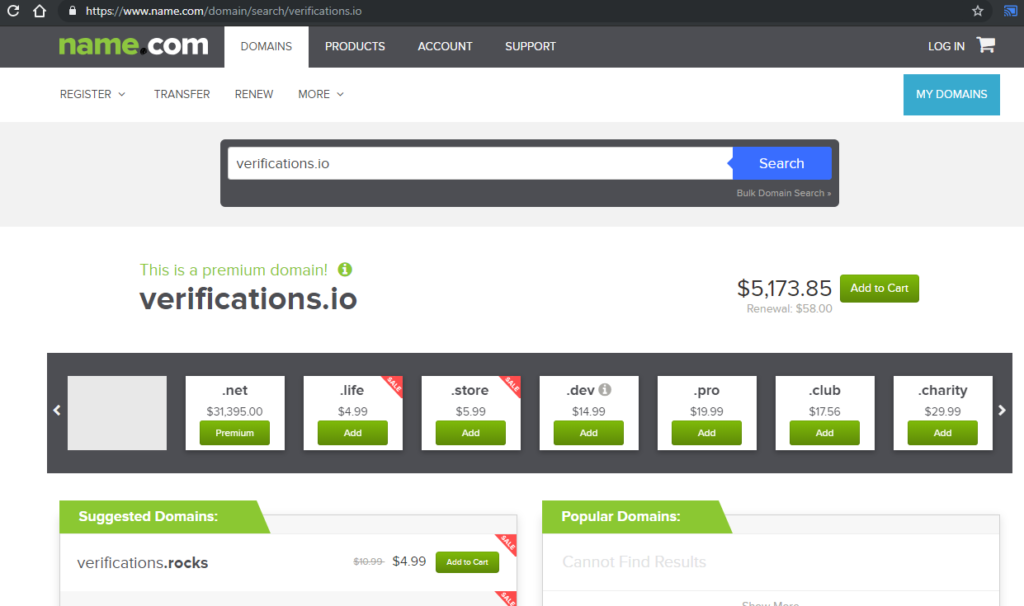
Verifications.io took down their website after the leak was uncovered and they have refused requests for a comment on the situation. Very few is known about the people behind the business with its backers maintaining their anonymity due to the dubious tactics it employs. Verifications.io domain is now available as a premium domain on Name.com for fresh registration in just around 5000 USD.
What was exposed in the email data breach?
All records contained the detailed profile information about the email owner. Millions of businesses profiles were also found in the email data breach. These records appear to mostly be made up of publicly available data. While no passwords were in the email data breach, all of the following were found:
- Email addresses
- Full names
- Gender
- Date of birth
- Residence Details
- Work and Designation etc.
How Verifications.io got your data?
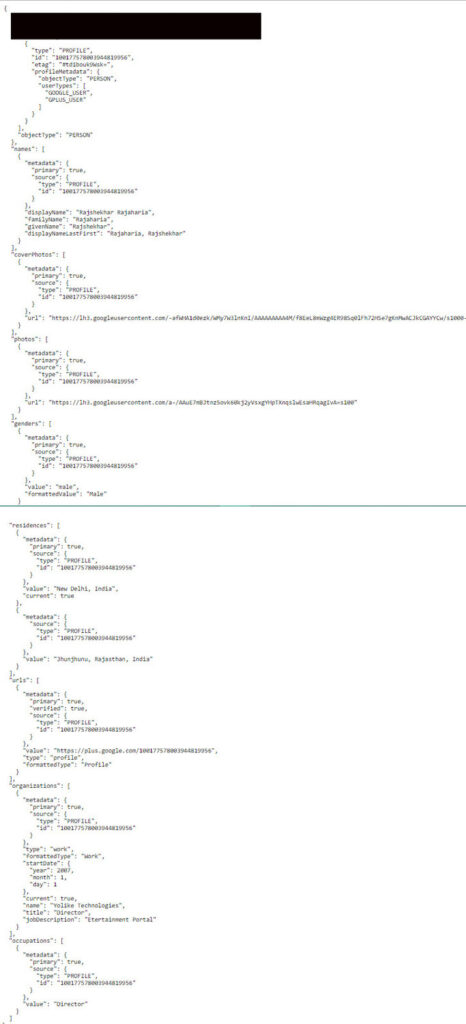
This is the trending question that how Verifications.io got your data? After doing a lot of research i found that thousands of these type of marketing agencies were using Google Picasa API to validate email address and to get detailed profile information about the email owner. Previously i also wrote two articles that how marketers and spammers were using Picasa Api to validate emails and to get detailed profile information about the email owner. Here is the Proof
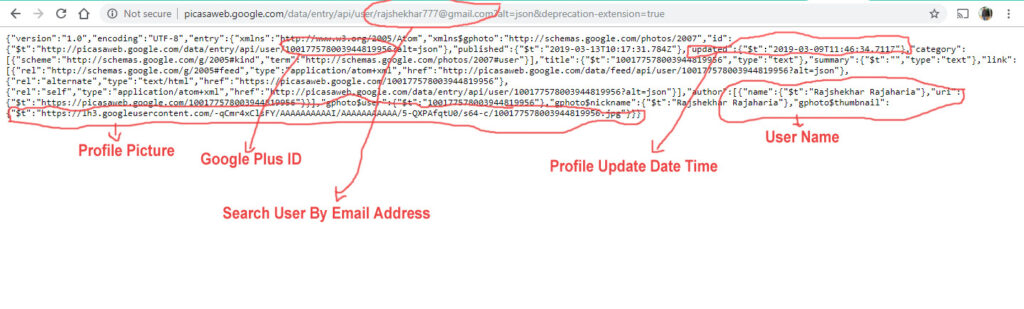
Picasa Web Albums Data API was giving a option to search any user profile detail by Email. Everyone was able to search any email id using Picasa API and Picasa API was returning their Name, Profile Update Time, Google Plus ID, Profile Picture and Album details etc. Google Apps or Business Accounts Details were also available their. Picasa API was a public API with no API Key or Token. There was no limit, People was able to request as much as they can. Anyone was able to fetch more than crores email’s data every day. You have Millions ,Billions Email IDs and their Google Plus ID. Now You can fetch further details via Google Plus API or Google People API using Google Plus ID. These API will return whole data like Gender, Education Details, Location, Work History, Designation etc etc. Now you have everything and you can use this data in any way.
Should you be worried?
Although the databases were accessible for some time, as soon as the problem was disclosed to Verifications.io, the service was taken offline and remains so. But marketing companies who having this data will start emailing in bulk. It also puts people at risk for robo calls and phishing attacks, which will try to lure even more personal information out of people.
Protecting Yourself
In light of this data breach, it’s more important than ever to take steps to protect yourself online. Here are some tips to help safeguard your personal information:
- Change Your Passwords: If you have an account with Verifications.io or any other website that may have been affected by the breach, be sure to change your passwords immediately. Use strong, unique passwords for each account to minimize the risk of unauthorized access.
- Monitor Your Accounts: Keep a close eye on your bank statements, credit reports, and other financial accounts for any suspicious activity. Report any unauthorized charges or transactions to your financial institution right away.
- Be Cautious of Unsolicited Emails: If you receive an email from an unknown sender or one that seems suspicious, do not click on any links or download any attachments. Delete the email and report it as spam to help protect yourself from potential phishing attempts.
Cash Matters
When it comes to protecting your personal information, cash is still king. Limit the amount of personal data you share online, and be cautious when providing sensitive information to websites or companies. Remember, it’s always better to be safe than sorry when it comes to safeguarding your privacy and security online.
Source: Linkedin,
Also Read: